I've been pretty quiet on my blog recently. I've been writing chapters for the upcoming ConfigMgr Current Branch Unleashed book and I'm looking forward to it being published towards the end of the year.
So, what's been going on? Deploying and managing Windows 10 has been a lot of fun recently. Microsoft have been promoting the enrollment of Windows 10 devices to be managed as mobile devices. There are several methods of accomplishing this such as:
- Azure Workplace Join (with Intune automatic enrollment)
- ConfigMgr On-premise MDM
So, what does it actually mean - managed as mobile devices? Beginning with Windows 8.1, Windows computers can also be enrolled and managed as mobile devices through the Open Mobile Alliance-Device Management (OMA-DM) channel. The OMA-DM standard is designed for managing mobile devices such as mobile phones and tablets. It is a lightweight specification and was designed to manage small foot-print devices, where memory, storage space, and bandwidth could be limited. Devices that use this standard are referred to as modern devices.
OMA-DM uses Open Mobile Alliance–Unified Resource Identifier (OMA-URI) values. Microsoft has led the way in publishing OMA-URI values that can be used to manage their devices using Intune. Useful examples of custom URI settings are available in this Microsoft document:
Custom URI settings for Windows 10 devices
More jargon - what is OMA-URI in English? Before that can become clear I need to introduce another term - Configuration Service Provider (CSP). CSPs expose device configuration settings in Windows 10. They provide an interface to read, set, modify, or delete configuration settings for a given feature and typically map to registry keys, files or permissions. CSPs are specific to a Windows 10 feature eg VPN CSP allows VPN configuration of a device. So, as promised, OMA-URI in English is:
"The full path to a specific configuration setting is represented by its OMA-URI. The URI is relative to the devices’ root node (MSFT, for example)".
It's clearer when you see an example:
This is a tree format diagram of the RemoteLock configuration service provider. The RemoteLock CSP supports the ability to lock a device that has a PIN set on the device or reset the PIN on a device that may or may not have a PIN set. This CSP is only supported in Windows 10 Mobile.
We can configure this feature using URIs as follows:
./Vendor/MSFT/RemoteLock/Lock
./Vendor/MSFT/RemoteLock/LockAndResetPIN
./Vendor/MSFT/RemoteLock/NewPINValue
./Vendor/MSFT/RemoteLock/LockAndResetPIN
./Vendor/MSFT/RemoteLock/NewPINValue
It's all pretty straightforward. Lets see a real world example. I want to stop users being able to unenrol their Windows 10 devices. This is very easy to configure using ConfigMgr Current Branch (you can do this with standalone Intune as well). You will need to have added an Intune subscription (even if you are using on-premise MDM). We will use the Policy CSP. There are a lot of settings that you can configure using this CSP. Have a look at this Microsoft document for details. You can see the settings and their supported Windows 10 editions.
Policy CSP
We are interested in this setting: Experience/AllowManualMDMUnenrollment. It's available for both desktop and mobile.
The URI full path is:
./Vendor/MSFT/Policy/Config/Experience/AllowManualMDMUnenrollment
Data type: Integer
Allowed values:
0 – not allowed
1 – allowed (default)
The process is carried out by creating and deploying Configuration Items in the ConfigMgr console.
Navigate to Assets and Compliance > Overview > Compliance Settings > Configuration Items
Right click Configuration Item and choose Create Configuration Item
On the General page, enter a name and description. Select "Windows 8.1 and Windows 10" in the "Settings for devices managed without the Configuration Manager client" section. Click Next.
Select all Windows 10 on the Supported Platforms page. Click Next.
On the "Device Settings" page, select "Configure additional settings that are not in the default settings groups". Click Next.
Click Add on the Additional Settings page.
Click Create Setting on the Browse Settings page.
Enter the required details on the "Create Setting" page. Click Apply and OK.
Back on the Browse Settings page choose your new setting and click Select.
Add the required value on the rules page and select OK.
The rule has now been configured. Finish the wizard to create the Configuration Item and then add to a Configuration Baseline. Finally deploy the Configuration Baseline to your devices.
So what does that look like on the client.
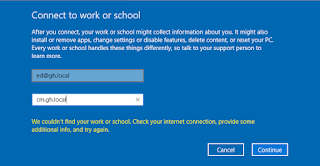
I've tried to remove the MDM management in this managed Windows 10 client but I'm unable to do so.
So, now that you've seen how easy this is try it yourself. Peter van der Woude has some cracking examples of managing Windows 10 features using OMA-DM:
Managing AppLocker on Windows 10 via OMA-DM
Setting up kiosk mode on Windows 10 via OMA-DM
Managing Windows Update for Business on Windows 10 via OMA-DM
Have a look at the full list of Configuration Service Providers. It's a impressive comprehensive list and you'll certainly find something that you can test in your lab.
Configuration service provider reference
I hope this blog was useful in explaining some of the new terminology. Until next time......