Microsoft Azure App Access Panel is pretty cool. I really like this technology. It is estimated that 25% of all software will be available on a SaaS (Software as a Service) delivery by 2020 (Forrester Application Adoption Trends: The Rise Of SaaS). Our users will continue to use Cloud Apps and the number will rise sharply. I previously blogged about the Azure Cloud App Discovery Tool. It's currently in Preview and involves installing an Endpoint Agent on user computers. Cloud App information is gathered and collated in a dashboard view by the Discovery Tool. See that blog here
So, as IT Professionals, what do we do with this information? We can use it to decide which Cloud Apps we will manage and deliver back to our users with this SaaS model. We will utilise Azure Active Directory to facilitate a single sign-on experience to these apps. Let's face it - each of us have multiple cloud identities that we have to manage so this is a cracking idea.
So how does it work. We will start in the Azure Portal. Launch the Portal and navigate to your Active Directory. Let's see how easy this is.
Open the Active Directory - "Users" is the default view. Click on the "Applications" tab.
See that we do not have any Application yet. Click to "Add an Application".
You are presented with three choices:
- Add an application my organization is developing - Microsoft will work closely with you to ensure that you can make your own applications available in the gallery.
- Add an application from the gallery - 2477 applications have already been added to the gallery and are available for use. This will be our choice in this demo.
- Publish an application that will be accessible from outside your network - use Azure AD Proxy to publish an on-premise application externally.
See that there are 2477 featured applications in the gallery. I'm just going to use 5 for my demo. Let's start with Twitter - you can use the search function.
Select Twitter and "click the tick" to continue.
Select "Assign Users".
For the purposes of the demo I will assign the app to users. However in production you would assign apps to groups of users. This feature is only available in Azure Active Directory Premium.Select your users and "Assign".
See that you can enter the app credentials on behalf of the user. This is very useful for shared accounts so that the credentials can be protected. "Click the tick" to continue.
I have now added my 5 applications and assigned them to users. What next?
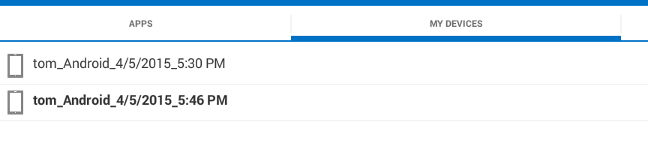
Your user should navigate to https://myapps.microsoft.com
and log in with their Active Directory credentials (remember they are synced with the Azure AD).......
...... and here we are. Say hello to the Microsoft Azure App Access Panel. See all the applications that have been assigned to this user. Note that Azure Active Directory Premium is required to assign more than 10 applications. Also it enables you to use corporate branding in the Panel.
Launch one of the applications. You will have to log in to each application for the first time only. Also you will be prompted to install the Access Panel Extensions once.
Select Install.
The Access Panel Extension wizard launches. Click Next to continue and install.
You now have to log in to the application for the first and only time.
Repeat this for each app (log in and enter credentials, no need to install the extensions again).
Now each time you open the Access Panel you can launch your apps without any further authentication.
Very cool and what a time saver.....
Remember that you need Azure AD premium licenses to make this technology work well for you. This is included in the Enterprise Mobility Suite.